Staying ahead in today’s fast-moving tech landscape isn’t just about keeping up with headlines—it’s about understanding which innovations will actually shape the way you build, secure, and optimize your systems. If you’re searching for clear, actionable insights on emerging Pax tech concepts, smart device advancements, and smarter network architecture, this article is designed to deliver exactly that.
Technology evolves in cycles, but the signals of meaningful change are often buried beneath hype. Here, we break down the most important innovation alerts, highlight practical optimization hacks, and explore how strategies like secure network segmentation are redefining modern infrastructure resilience. Whether you’re refining device ecosystems or rethinking connectivity frameworks, you’ll find focused analysis aligned with real-world implementation.
Our insights are grounded in continuous industry monitoring, technical research, and hands-on evaluation of evolving network and device technologies—so you can move from awareness to action with confidence.
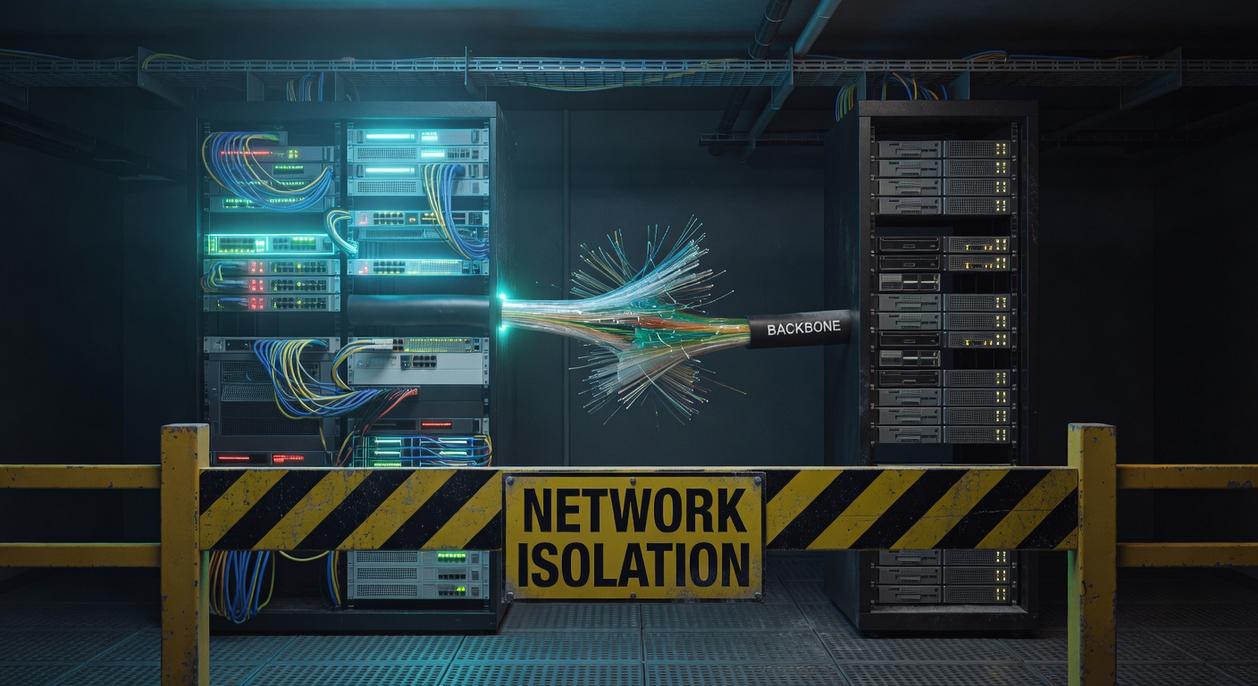
Contain the Blast Radius
A flat network means every device can talk to every other device. In practice, that’s like leaving every door unlocked in an office building (convenient, until it isn’t).
First, inventory your assets: servers, user devices, IoT gear, and critical databases. Next, group them by function and sensitivity. For example, finance systems should never share unrestricted access with guest Wi‑Fi.
Then implement secure network segmentation using VLANs and internal firewalls. Apply least privilege rules so only required ports and protocols are allowed.
Finally, test by simulating a breach and verifying traffic is contained. Adjust rules as needed.
Choosing Your Segmentation Model: From VLANs to Microsegmentation
Perimeter-Based Segmentation (The Traditional Fort) relies on edge firewalls to build a hardened outer wall. The benefit is simplicity: one choke point, clear rules, and fast deployment. However, once an attacker slips inside, lateral movement can spread quickly (think Trojan horse, but digital).
Next, VLAN Segmentation (The Foundational Layer) logically groups devices to isolate traffic—separating guest Wi-Fi from corporate systems, for example. This reduces broadcast noise and limits accidental exposure, giving teams cleaner performance and safer collaboration.
Then comes Firewall-Based Segmentation (Internal Zoning). By creating secure zones for Finance, HR, and Development, you contain breaches and protect sensitive data. The payoff? Tighter compliance and clearer audit trails.
Finally, Microsegmentation (The Zero-Trust Evolution) isolates individual workloads, especially in cloud environments. This granular control strengthens secure network segmentation, minimizes blast radius, and boosts resilience. Pro tip: start with high-value assets first to maximize impact.
The Blueprint: How to Plan Your Network Segmentation Project
If there’s one hill I’ll die on in cybersecurity, it’s this: you can’t secure what you can’t see. That’s why Step 1—asset discovery and traffic analysis—isn’t optional. It’s foundational. Map every device, application, and data flow. Yes, even that “temporary” IoT sensor someone plugged in six months ago. Shadow IT is real (and it’s usually where trouble starts). Use automated discovery tools and review traffic logs to understand who’s talking to whom and why.
Step 2 is defining your segments. Group assets by:
- Function (Production Servers vs. Development Sandbox)
- Risk level (IoT Devices vs. Core Databases)
- Compliance needs (PCI, HIPAA, etc.)
Logical zones reduce blast radius—meaning if one segment is compromised, the attacker can’t roam freely like it’s an open-world video game.
Step 3 is where strategy sharpens: architect your access policies. Apply the principle of least privilege (a security concept where users and systems get only the access absolutely necessary—nothing more). Define the “who, what, where, when, and why” for every connection. In my opinion, overly permissive rules are the silent killer of otherwise solid architectures. Secure network segmentation only works when enforcement is strict.
Finally, Step 4: choose your technology. VLANs work for basic isolation. Next-generation firewalls add deeper inspection. Microsegmentation platforms provide granular, workload-level control. Your choice should reflect your risk tolerance, budget, and growth plans—especially if you’re scaling into environments tied to understanding 5g network infrastructure and deployment.
Pro tip: test policies in staging before full rollout. Broken access rules disrupt business faster than breaches.
From Theory to Practice: A Step-by-Step Implementation Guide
Turning network segmentation from a diagram into a working system can feel intimidating. However, when you break it into clear phases, the process becomes manageable and far less risky.
1. Configure Your Network Infrastructure
First, create VLANs (Virtual Local Area Networks—logical groupings of devices within the same physical network). On your switch, define VLAN IDs and assign ports accordingly. Next, configure corresponding sub-interfaces on your router or firewall, tagging each with the correct VLAN ID and IP subnet. For example, VLAN 10 might serve Corporate (192.168.10.0/24), while VLAN 20 supports Guests (192.168.20.0/24). This foundation enables secure network segmentation by separating traffic at Layer 2 and Layer 3.
2. Write and Deploy Firewall Rules
Once traffic is segmented, define access control lists (ACLs—rule sets that permit or deny traffic). For instance:
- Deny: Guest VLAN → Corporate VLAN
- Allow: Corporate VLAN → Internet
- Allow: IT VLAN → All VLANs (management only)
Be explicit. “Implicit deny” (blocking everything not explicitly allowed) reduces surprises later. Pro tip: Document every rule’s purpose to avoid future confusion.
3. Test and Validate in a Staging Environment
Before production, simulate real workflows. Can employees access shared drives? Are printers reachable? One hospital, for example, discovered blocked medical device traffic during testing—catching it early avoided downtime.
4. Phased Rollout and Monitoring
Finally, roll out gradually, starting with low-risk segments. Use monitoring tools to review logs, detect violations, and confirm policies behave as intended. In short, trust your design—but verify relentlessly.
Sustaining a Secure Architecture: Long-Term Segmentation Best Practices
Segmentation is not a “set and forget” control. Regular audits and rule reviews keep environments clean and defensible. Schedule quarterly firewall rule assessments to remove obsolete entries, validate segment classifications, and confirm that new applications are properly isolated. Stale rules create hidden pathways attackers love (think of them as forgotten spare keys).
Automation strengthens secure network segmentation by reducing human error. Policy orchestration tools standardize rule deployment across firewalls, SD-WAN, and cloud environments, ensuring consistency at scale. The benefit? Faster changes, fewer misconfigurations, and measurable compliance alignment.
Integrating segmentation with Identity and Access Management (IAM) ties access to verified user roles, not just IP addresses. When HR systems update a role, network permissions adjust automatically—limiting lateral movement risks.
Finally, maintain clear network diagrams and policy documentation. Detailed records accelerate troubleshooting, simplify audits, and support regulatory requirements. Pro tip: version-control your diagrams to track architectural drift over time.
Building a Resilient and Defensible Network
A flat, unsegmented network is like an office without walls—once an intruder gets in, every room is exposed. Attackers rely on lateral movement (the ability to hop from system to system after initial access) to escalate damage. The fix isn’t guesswork; it’s deliberate, secure network segmentation.
Key implementation features include:
- Asset discovery and traffic mapping for visibility
- Policy-driven access controls that restrict east-west movement
- VLANs and firewalls that enforce zone boundaries
These technical controls create defensible zones, reducing blast radius and downtime. Start with discovery today—map traffic flows and turn insight into immediate risk reduction.
Take Control of Your Network’s Future
You came here looking for clearer insight into strengthening your infrastructure, optimizing performance, and protecting your systems from evolving threats. Now you have a practical understanding of how smarter architecture, automation, and secure network segmentation work together to reduce risk and boost efficiency.
The real pain point isn’t just slow systems or scattered devices — it’s the hidden vulnerabilities and missed optimization opportunities that cost you time, money, and trust. Ignoring them only makes scaling harder.
Your next move is simple: assess your current setup, identify weak points in traffic flow and access control, and implement secure network segmentation alongside smarter optimization strategies. Don’t wait for a breach or bottleneck to force action.
If you’re ready to eliminate blind spots and future-proof your infrastructure, start applying these strategies today. Join thousands of tech leaders already leveraging advanced network insights to stay ahead. Strengthen your systems now and turn your network into a competitive advantage.
